How To Hack Your Phone To Get Unlimited
Today, smartphones have become a mini replica of a fully functional computer. A smartphone has wifi connectivity, web browsing capabilities and the ability to run applications that provide a wide range of functions. That's great news for consumers who have active online lifestyles.
But there'south bad news too—smartphones have become a data treasure for hackers. It's a target that'south difficult for them to ignore. For example, hackers use smartphones every bit "entry points" to attack banks or other organizations for data. They send malicious messages from the victim'southward phone - making the user accountable for the theft.
Hackers do not even have to steal the victim'south phone to download malware. They just have to plant viruses on websites designed to infect the smartphones and expect for the user to just click a link on their phone. Such hidden mobile applications accounted for half of consumer mobile threats in 2019.
6 Signs That Confirm Your Smartphone Has Already Been Hacked
If your smartphone is displaying one or more than of the following unusual behavior, in that location is a possibility that your device has already been hacked.
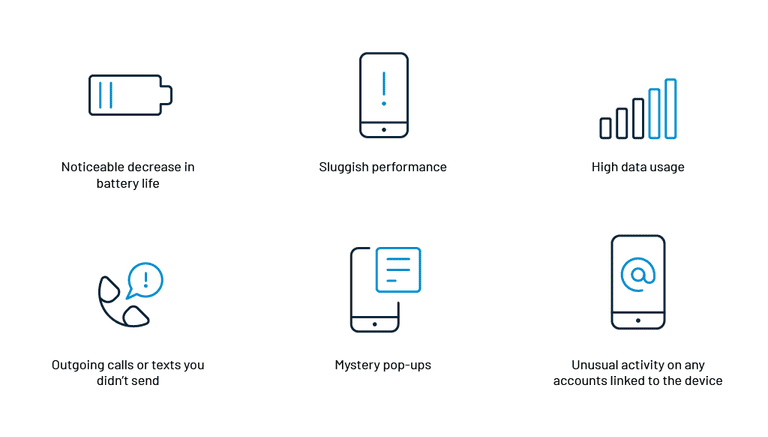
1. Noticeable decrease in battery life
If your phone has been compromised by malware, the battery will drain faster than usual. This is because the malware uses the phone's resource to transmit sensitive data back to the hackers' server. Then, if the phone usage habits accept remained the same, but a noticeable and constant subtract in battery life is seen, so hacking may be the reason.
2. Sluggish performance
Malware and other hacking tools work in the background while using the smartphone'south resources and battery power. This reduces performance significantly. Unexpected freezing of apps or crashes, phone restarting, or device heating up are as well the signs that you need to go on an center out for.
three. High information usage
Unusually high information usage past a smartphone can be a sign of hacking. Malicious software might be using information in the groundwork to record activities and ship information to the hacker.
4. Outgoing calls or texts you didn't send
Strange behavior like outgoing calls or texts, which take not been sent by the smartphone user, tin exist hackers tapping into the telephone. These calls or texts could exist premium-rate numbers that malware is forcing your smartphone to contact. The earnings would be directed to the hacker's account.
v. Mystery pop-ups
Constant popular-up alerts could indicate that the smartphone has been infected with adware, a form of malware. Hackers apply adware to force users into viewing web pages that bulldoze revenue through clicks. While all pop-ups are not necessarily malware attacks, some may likewise be phishing attempts to concenter users to give away sensitive data.
6. Unusual activity on whatever accounts linked to the device
If the telephone has been hacked, hackers would exist able to admission social media, e-mail, or apps, putting yous at risk for identity fraud. Activities such every bit resetting passwords, emails being sent or read without the users' knowledge, or new account sign-ups are all signals which indicate that the phone is in the wrong hands.
What to Do if Your Telephone Is Hacked
If you lot witness whatever of the to a higher place signs on your smartphone, in that location is a high possibility that your telephone has been hacked. Y'all demand to take the advisable steps to eliminate the malware that has attacked your phone. Some of the steps which you can follow are:
- Download a mobile security app from a trusted site, which not simply scans for malware but offers boosted features like a telephone call blocker, firewall, VPN and a feature to request PIN for accessing sensitive apps like online banking.
- Change passwords as shortly as possible.
- Remove suspicious apps.
- Inform friends and contacts that you have been hacked. This warning would aid your contacts ignore suspicious messages sent past the malware to their phones.
- Carry out an in-depth maintenance check from your smartphone shop.
- If everything fails, a manufacturing plant reset volition assistance to sort the problems.
viii Ways To Stop Someone From Hacking Your Telephone Again
Many smartphone users believe that their mobile service providers should deploy cyber-protection. However, it is also the responsibility of the users to protect themselves from hackers. In that location are many dissimilar ways a hacker tin get into your phone and steal personal and critical data.
Here are a few safety tips to ensure that you lot do not become a victim of phone hacking:
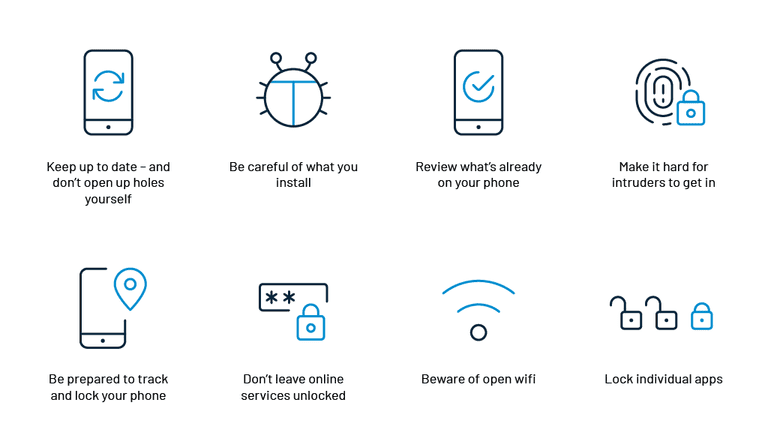
1. Go on up to engagement – and don't dig in holes yourself.
Phones work on the aforementioned principle as a computer operating arrangement. Whenever software updates for phone operating systems are available, users need to become their phones updated directly from the manufacturer'south website. Hackers exploit vulnerabilities in out-of-date operating systems. Therefore, downloading the latest patches would be of great help in keeping your phone rubber.
ii. Be conscientious of what you lot install.
Installation of whatever smartphone app requires users to grant permissions, including reading files, access the camera, or listening to the microphone. There are legitimate uses for these capabilities, but they're potentially open to misuse. Users demand to be conscientious before blessing such requests. Always download apps from a trusted source.
3. Review what's already on your phone.
Users demand to keep track of the apps already downloaded on their smartphones. It may have been rubber when installed the first fourth dimension, but subsequent updates could have infected the smartphone. Always keep track of what permissions have been given to the apps while accessing the operating organization of the smartphone. Diverse security apps would have helped provide an overview of the permissions, only users demand to download such apps from trusted sites.
4. Go far hard for intruders to become in.
Users should ensure that they continue their phone locked when not in utilize and also ready a strong passcode. Smartphones are basically like computers, and hence, need antivirus and malware protection. Install a good antivirus bundle onto your smartphones to make information technology difficult for hackers to get in. Apply lock patterns, facial recognition or phonation recognition to add together an extra level of access security for your smartphone.
5. Be prepared to runway and lock your phone.
Services like 'notice my device' are provided past smartphone manufacturers to help users locate their stolen phone on a map and remotely erase their information. All users need to do is fix their phone to automatically erase itself after a certain number of incorrect access attempts. It is also possible to make a phone ring fifty-fifty if it is kept on silent. It is helpful in tracking down phone that was simply stolen.

6. Don't leave online services unlocked.
Auto-login is a convenient characteristic that automatically logs in without entering the password every bit they are already saved in the browser. It is a huge security risk considering hackers simply demand to open the browser to access all the online accounts. Instead of using auto-login features, users should use a countersign manager app that requires them to re-enter a master countersign regularly.
7. Beware of open wifi.
Using an open wireless network allows anyone in the vicinity to snoop on what you are doing online. At times, hackers open their own gratis wireless "hotspots" to concenter users to admission their wifi. Once connected, they tin can easily hack into phones.
And then, whenever yous are non sure nearly the security of the wireless network, use your telephone's mobile internet connection. Information technology will be a much safer and secure option. Users can also opt for VPN tools which route the traffic through a private encrypted channel. Turning on two-gene authentication for online accounts will too assist protect your privacy on public wifi. Users should plow off bluetooth and personal hotspot functions when non required.
8. Lock individual apps.
Locking your phone is important but as a secondary security measure, lock individual apps besides. This adequacy can be implemented by using apps from a trusted source as they are not an inbuilt feature of the operating system.
Conclusion
Smartphones have become an essential part of our daily lives. Once you know about how your phone can be hacked, you can accept various safety precautions to protect it from data theft. Furthermore, it will also keep your data secure from opportunist thieves or country-sponsored spies!

How To Hack Your Phone To Get Unlimited,
Source: https://www.loginradius.com/blog/identity/how-to-stop-phone-hacking/
Posted by: talamantesunis1993.blogspot.com


0 Response to "How To Hack Your Phone To Get Unlimited"
Post a Comment